Our previous article examined the benefits of Palo Alto Networks Firewall Single Pass Parallel Processing (SP3) architecture and how its combine with the separate Data and Control planes to boost firewall performance and handle large amounts of traffic without and performance impact. This article focuses on the traffic flow logic inside the Palo Alto Firewall and two unique features that separate it from the competition: Application-based policy enforcement (App-ID) & User Identification (User-ID).
For more Technical articles on Palo Alto Networks Firewalls, visit our Palo Alto Networks Firewall Section
FLOW LOGIC OF THE NEXT-GENERATION FIREWALL
The diagram below is a simplified version of the flow logic of a packet travelling through a Palo Alto Networks Next-Generation Firewalland this can be always used a reference to study the packet processing sequence:
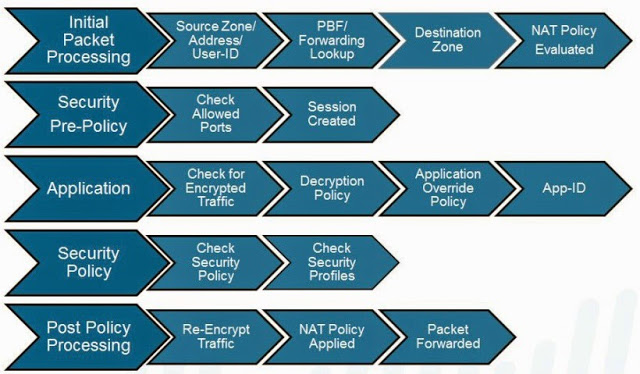
Figure 1. Flow Logic of a packet inside the Palo Alto Networks Next Generation Firewall
Palo Alto Networks Next-Generation Firewalls works with the concepts of zones not interfaces, once a packet enters the firewall, the Palo Alto Networks Next-Generation Firewalls identifies from which zone the packet came and where it is destined to go. This is similar to Cisco IOS Routers Zone-based Firewalls and Cisco ASA Firewalls.
Users interested can also download for free the Palo Alto Networks document “Day in the Life of a Packet” found in our Palo Alto Networks Download section which explains in great detail the packet flow sequence inside the Palo Alto Networks Firewall.
APP-ID & USER-ID – FEATURES THAT SET PALO ALTO APART FROM THE COMPETITION
App-ID and User-ID are two really interesting features not found on most competitors’ firewalls and really help set Palo Alto Networks apart from the competition. Let’s take a look at what App-ID and User-ID are and how they help protect the enterprise network.
APP-ID: APPLICATION-BASED POLICY ENFORCEMENT
App-ID is the biggest asset of Palo Alto Networks Next-Generation Firewalls. Traditional firewalls block traffic based on protocol and/or ports, which years ago seemed to be the best way of securing the network perimeter, however this approach today is inadequate as applications (including SSL VPNs) can easily bypass a port-based firewall by hopping between ports or using well-known open ports such as tcp-http (80) or tcp/udp-dns (53) normally found open.
A traditional firewall that allows the usage of TCP/UDP port 53 for DNS lookups, will allow any application using that port to pass through without asking second questions. This means that any application can use port 53 to send/receive traffic, including evasive applications like BitTorrent for P2P file sharing, which is quite dangerous:
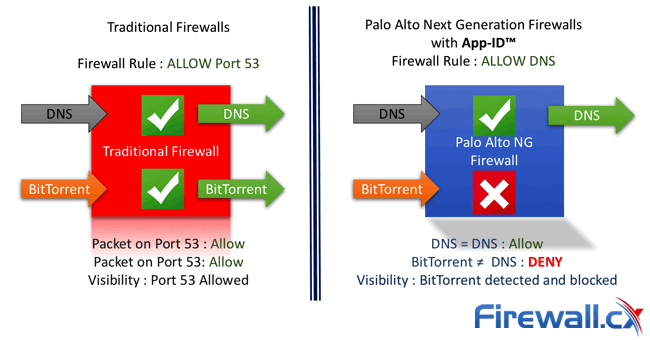
Figure 2. Palo Alto Network’s App-ID effectively blocks unwanted BitTorrent traffic
With App-ID, Palo Alto Networks Next-Generation Firewalls uses multiple identification mechanisms to determine the exact identity of applications traversing the network. Following is the order in which traffic is examined and classified:
- Traffic is classified based on the IP Address and port
- Signatures are then applied to the allowed traffic to identify the application based on unique application properties and related transaction characteristics.
- For evasive applications which cannot be identified though advance signature and protocol analysis Palo Alto Networks Next-Generation Firewalls applies heuristics or behavioral analysis to determine the identity of the application.
Using the above process Palo Alto Networks Next-Generation Firewalls are very successful in identifying DNS traffic not only at the port level but also at the Application level, making it extremely difficult for an evasive application like BitTorrent to use any open ports and pass through the firewall undetected.
USER IDENTIFICATION (USER-ID)
User-ID is one more key determining factor that places Palo Alto Networks Next-Generation Firewalls apart from the competition.
Traditionally, security policies and rules were applied based on IP addresses. However, these days both the users and applications have a dynamic nature which means that IP addresses alone have become inefficient for monitoring and controlling user activity. A single user might access the network from multiple devices (laptops, tablets, smartphones, servers).
Thanks to the User-ID feature of the Palo Alto Networks Next-Generation Firewalls administrators are able to configure and enforce firewall policies based on users and user groups instead of network zones and addresses.
The Palo Alto Networks Next-Generation Firewall can communicate with many directory servers, such as Microsoft Active Directory, eDirectory, SunOne, OpenLDAP, and most other LDAP-based directory servers to provide user and group information to the firewall. With this powerful feature, large organizations are able to create security policies that are user or group based, without worrying about IP addresses associated to them.
THREAT PREVENTION
Palo Alto Networks Next-Generation Firewalls are very effective in preventing threats and they do offer real-time threat prevention from viruses, worms, spyware, and other malicious traffic can be varied by application and traffic source.
APPLICATION COMMAND CONTROL (ACC)
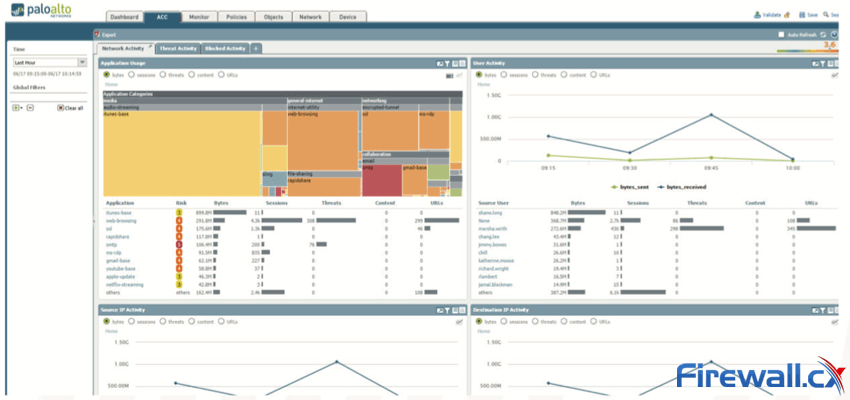
Palo Alto Networks Next-Generation Firewalls offer the most interactive graphical summary of the applications, URLs, users, threats, and content traversing the network. The ACC makes use of the firewall logs to provide the visibility of the traffic patterns, information on threats, user activity, Rule usage and many other information in an interactive graphical form:
Figure 3. Palo Alto Application Command Center provides maximum visibility on network traffic (click to enlarge)
CONCLUSION
This article why Palo Alto Networks Next-Generation Firewalls are really unique in many terms. Features such as App-ID and User-IDallow in-depth control of applications and users, making it possible to fully manage small to very large enterprises without a problem. The Application Command Control (ACC) helps give the administrator a complete view of applications and services accessing the internetalongside with some very useful statistics.
No comments:
Post a Comment